- May 5, 2023
- Posted by: Surender Kumar
- Category: PowerShell
Enable BitLocker without TPM PIN
If you are looking for a way to enable BitLocker drive encryption with PowerShell without using any TMP PIN, you are on the right page. In this post, you will learn how to use PowerShell to enable BitLocker with TPM protector alone. The only prerequisite is that your computer need to have a valid TPM hardware but since you’re already on this page, I assume your computer meets that prerequisite.
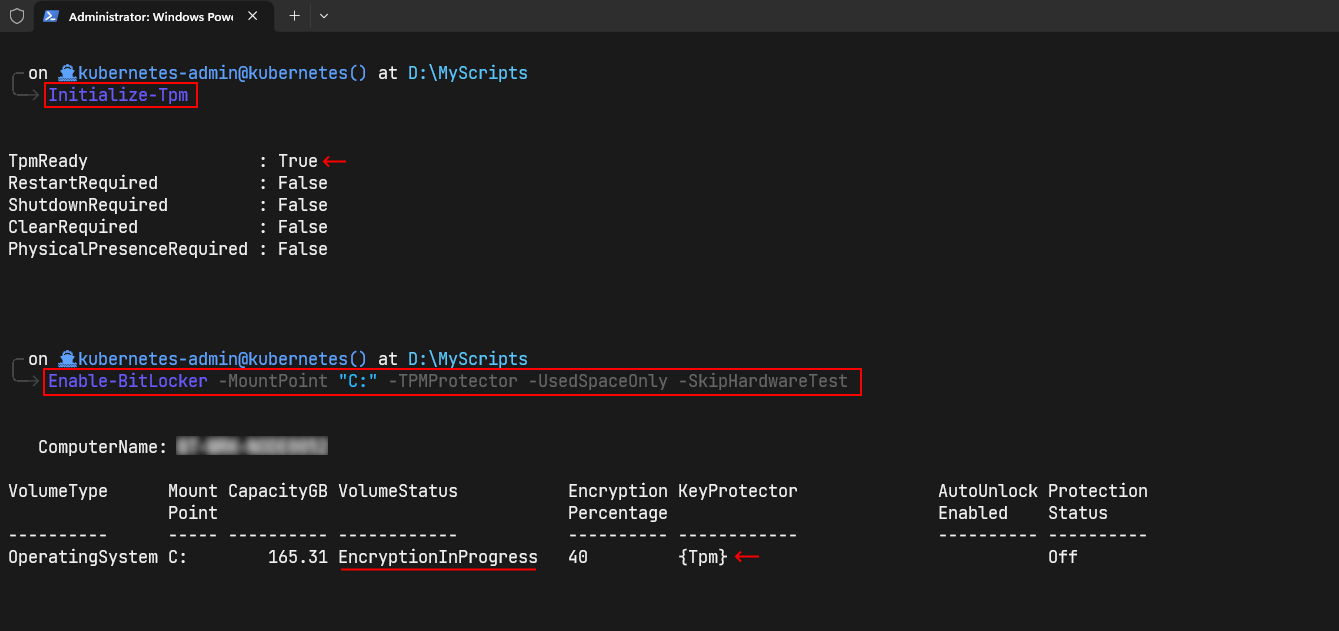
To enable BitLocker, launch an elevated PowerShell prompt and run the following commands:
Initialize-Tpm Enable-BitLocker -MountPoint "C:" -TPMProtector -UsedSpaceOnly -SkipHardwareTest
If you omit the -SkipHardwareTest parameter, it will ask you to restart your computer for a hardware test and the BitLocker encryption will start after the restart. Although it is possible to use TPM protector alone without any additional key protectors, I always recommend adding an additional key protector (such as a PIN or a startup key) so that you don’t lose your data in case something goes wrong with the TPM hardware. Having additional protector in place also saves you from BitLocker encryption bypass attacks, where a skilled attacker with physical access to your computer could gain access to your data.
Troubleshooting
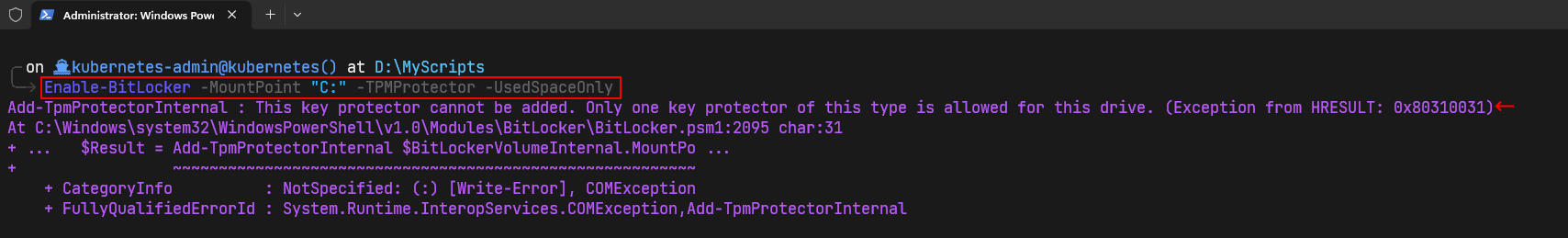
You may get the following error while enabling BitLocker with PowerShell on the operating system drive:
Add-TpmProtectorInternal : This key protector cannot be added. Only one key protector of this type is allowed for this drive. (Exception from HRESULT: 0x80310031)
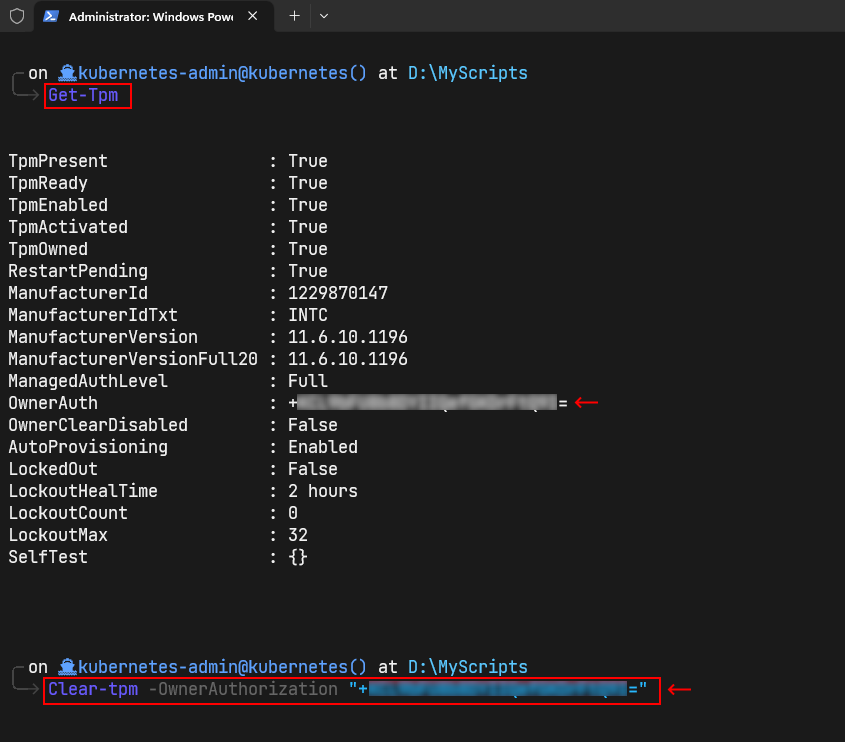
If you get this error, you need to clear the TPM with these commands:
Get-Tpm Clear-Tpm -OwnerAuthorization "ownerauth_value_returned_by_above_command" Restart-Computer -Force
After restarting your computer, you can start over again. I hope this post helps. To learn how to use BitLocker with PowerShell in more details, check out my BitLocker with PowerShell series.