- September 10, 2016
- Posted by: Surender Kumar
- Category: PowerShell
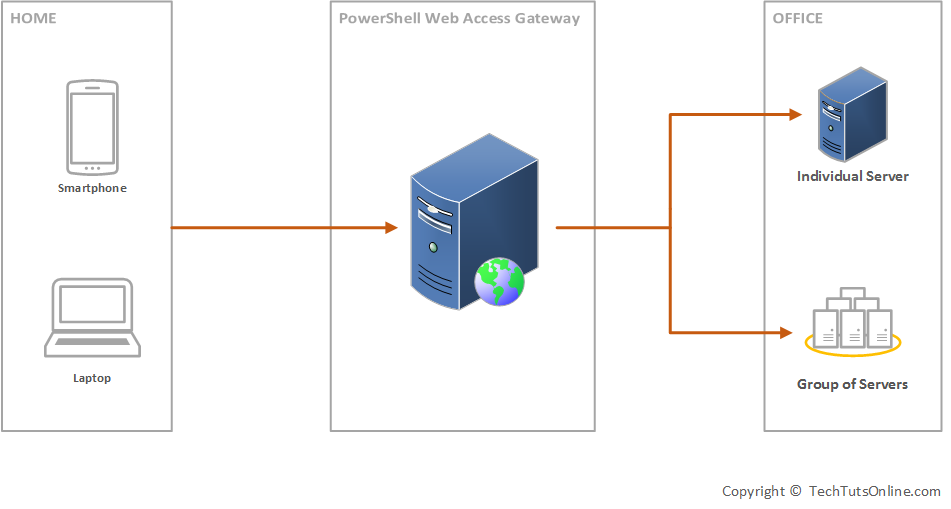
Windows PowerShell Web Access (WPWA) was first introduced in Windows Server 2012. PowerShell Web Access requires a Server 2012 computer to act as a Windows PowerShell gateway, providing a web-based Windows PowerShell console that is targeted at a remote computer. It enables IT Pros to run Windows PowerShell commands and scripts from a Windows PowerShell console in a web browser, with no Windows PowerShell, remote management software, or browser plug-in installation necessary on the client device. All that is required to run the web-based Windows PowerShell console is a properly-configured Windows PowerShell Web Access gateway, and a client device browser that supports JavaScript and accepts cookies.
By using PowerShell Web Access, you can use your personal laptops, borrowed computers, tablet or even your mobile, that are not running a Windows-based operating system. IT Pros can perform critical management tasks on remote Windows-based servers from devices that have access to an Internet connection and a web browser. The only component required is the PowerShell Web Access Gateway. It is amazing. Isn’t it?
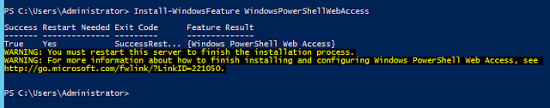
Follow the steps to install PSWA on a server:
Step 1: Add Windows PowerShell Web Access role on server. Open Windows PowerShell and type the following command:
Install-WindowsFeature -Name WindowsPowerShellWebAccess -Computername <server-name> -IncludeManagementTools -Restart
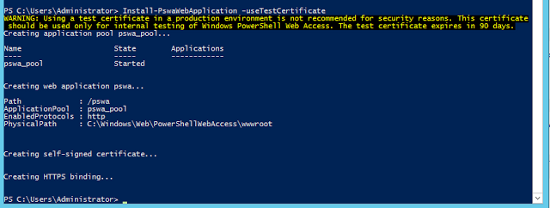
 Step 2: Configure the Windows PowerShell Web Access Gateway
Step 2: Configure the Windows PowerShell Web Access Gateway
You should use a valid SSL certificate if you are deploying this to your production environment. Since I am doing this is a test lab, I will use Test Certificate which is valid for 90 days.
Type the following command:
Install-PswaWebApplication -useTestCertificate
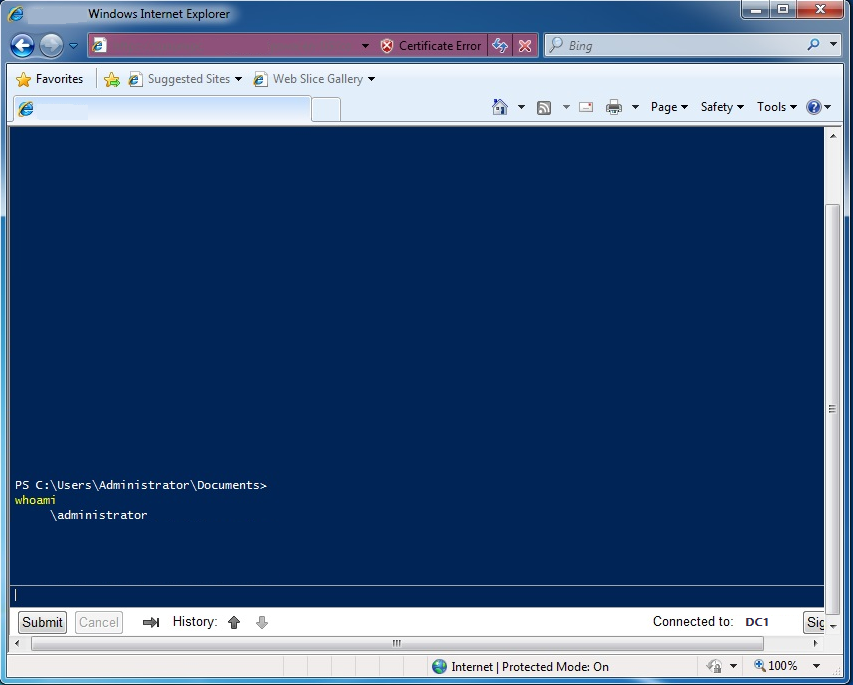
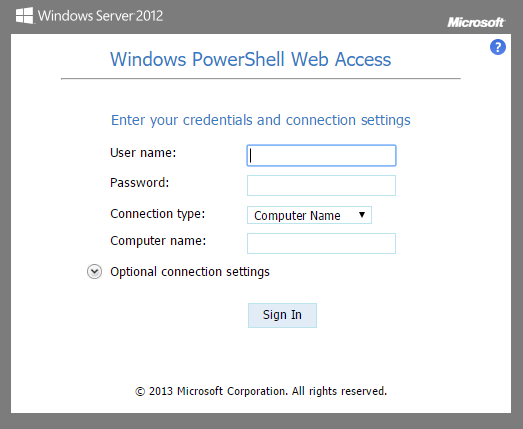
 When you have completed these steps, you should be able to open the web-based console sign in page by visiting https://192.168.0.3/pswa or https://gateway_server/pswa
When you have completed these steps, you should be able to open the web-based console sign in page by visiting https://192.168.0.3/pswa or https://gateway_server/pswa
 Now, set the authorization rule on which all can have rights for PowerShell Web Access. If you are configuring this in your production environment, never use * under authorization rule. Instead you must specify a specific computer or group, specific user or group. For my test lab, I will set the ComputerName to DC1 and UserName to admin. If you specify *, it means all computers and all users of my domain will have full access to run any PowerShell command. This is a very dangerous authorization rule and should never been used in production environment.
Now, set the authorization rule on which all can have rights for PowerShell Web Access. If you are configuring this in your production environment, never use * under authorization rule. Instead you must specify a specific computer or group, specific user or group. For my test lab, I will set the ComputerName to DC1 and UserName to admin. If you specify *, it means all computers and all users of my domain will have full access to run any PowerShell command. This is a very dangerous authorization rule and should never been used in production environment.
Add-PswaAuthorizationRule -ComputerName DC1 -UserName admin -ConfigurationName AdminsOnly
Now you can login via admin user account to DC and you can run any PowerShell command as you generally run locally. The browser console also gives you Tab key to perform tab completion.