- January 30, 2017
- Posted by: Surender Kumar
- Category: Windows Server
Creating Custom Attributes In Active Directory
Table of Contents
The schema is the Active Directory component that defines all the objects and attributes that the directory service uses to store data. The physical structure of the schema consists of the object definitions. The schema itself is stored in the directory. By default, Active Directory schema contains all the attributes that are essential for every organization. But there is a BUT. Every organizational requirements are different. Any organization may want to add some attributes that are not available in Active Directory Schema by default. For example, you are working as Server Administrator in a large School (or institute for that matter) and you are asked to add some Custom Attributes for Students like Grade, Courses, and Campus Name etc. In such situation, extending the Active Directory Schema comes handy.
In the following article, I will look into How to add custom attributes in Active Directory.
Note: Since modifying the AD schema may involve Registry editing and use of some low level editors like ADSIEdit, the following procedure requires that you understand what you are doing. Another important thing to note is that modifying Active Directory Schema is not reversible. The attributes once added will remain in Active Directory forever and cannot be removed easily.
If you’re beginner in Active Directory and Windows Registry editing, I would recommend you to learn the Basics first. I will not be responsible for any loss or damage caused during this exercise. If you are good to go, make sure you try this in a test lab environment first (not in production).
To learn how to create and manage custom AD attributes using PowerShell, please checkout this article. If you want to do it using GUI tools, please continue reading this article.
Permissions and Requirements
- Schema changes require the Schema Master role holder DC to be online and available.
- You must be a member of Schema Administrators or Enterprise Administrators group.
- I would recommend performing this operation on Schema Master role holder DC.
Allow Schema Updates
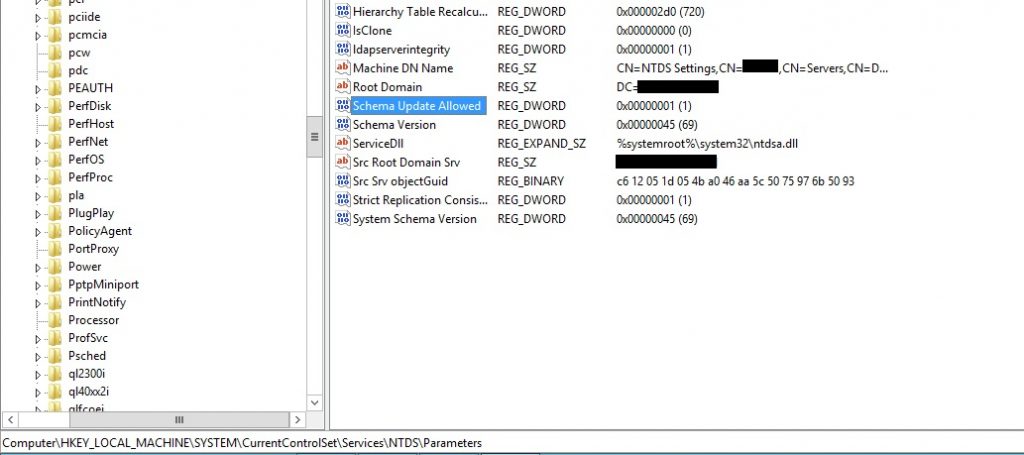
- Open regedit.
- Go to the HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\NTDS\Parameters registry entry.
- Create a REG_DWORD (32-bit) value and name it Schema Update Allowed.
- Set the value to 1.
- Click OK.
- Close the registry editor.
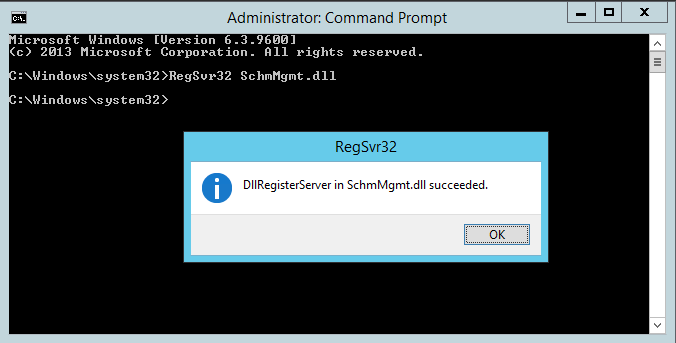
Register Schema snap-in
- Open cmd as administrator.
- Type RegSvr32 SchmMgmt.dll command and hit enter.
- You should get the DllRegisterServer in SchmMgmt.dll succeeded
Adding Custom Attributes
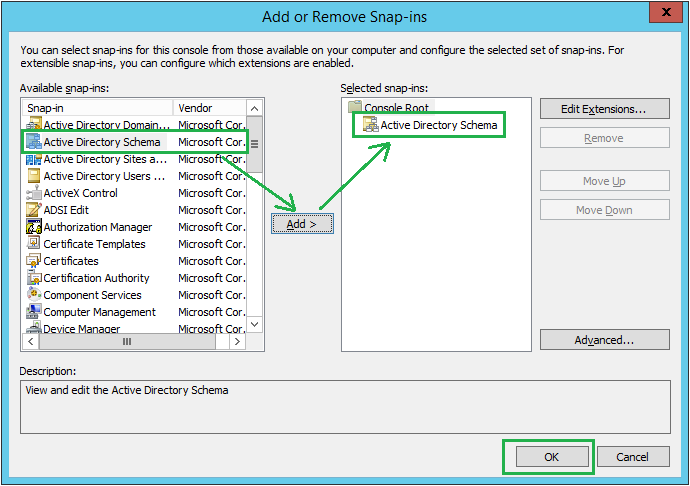
- Press the keys ‘Windows‘ + ‘R‘ to open Run dialog.
- Type in mmc and hit enter.
- Go to File -> Add/Remove snap-in… or simply press the keys ‘Ctrl’ + ‘M’ to open Add/Remove snap-in.
- Select the snap-in Active Directory Schema, click Add >, and click the button OK.
5. Expand the Active Directory Schema option, right-click the Attributes and click Create Attribute.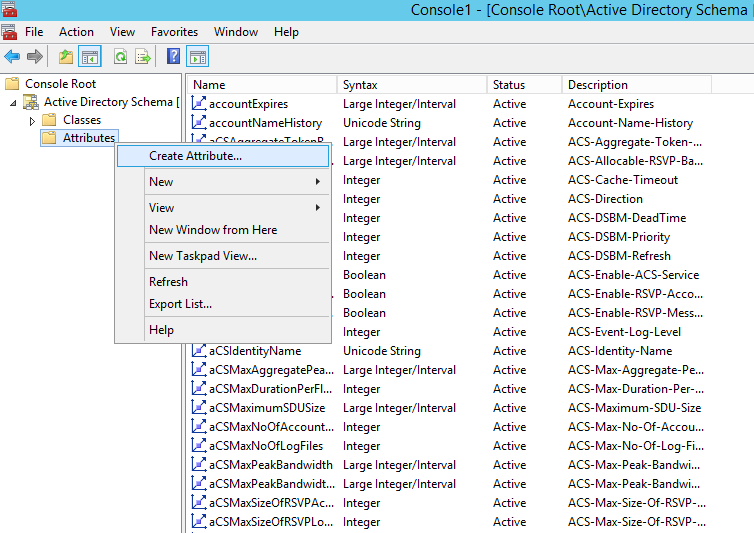
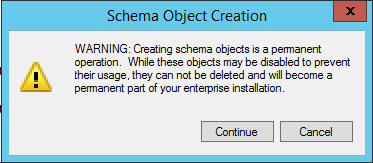
6. You will receive Schema Object Creation warning message indicating that creating schema objects is a permanent operation. Click Continue to proceed.
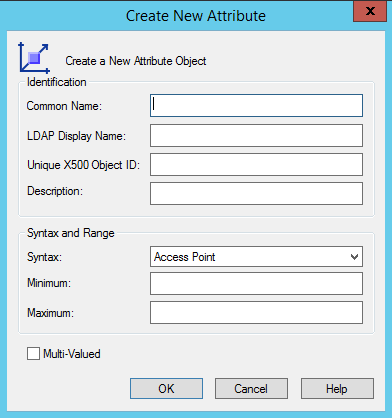
7. Now you will see the following Create New Attribute window.
8. Enter the Common Name, LDAP Display Name. For example, if you want to create a custom attribute with the name Campus Name, type in Campus Name in Common Name field and campusName in LDAP Display Name field. Note that LDAP Display Name field does not contain empty space.
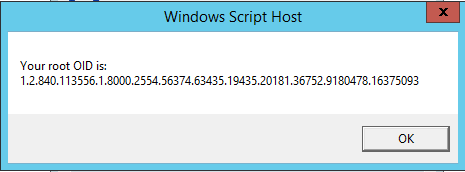
9. Unique X500 Object ID or OID field will contain the unique ID of object. To generate the OID, copy the following code and save it to a .vbs file.
Function GenerateOID()
'Initializing Variables
Dim guidString, oidPrefix
Dim guidPart0, guidPart1, guidPart2, guidPart3, guidPart4, guidPart5, guidPart6
Dim oidPart0, oidPart1, oidPart2, oidPart3, oidPart4, oidPart5, oidPart6
On Error Resume Next
'Generate GUID
Set TypeLib = CreateObject("Scriptlet.TypeLib")
guidString = TypeLib.Guid
'If no network card is available on the machine then generating GUID can result with an error.
If Err.Number <> 0 Then
Wscript.Echo "ERROR:Guid could not be generated, please ensure machine has a network card."
Err.Clear
WScript.Quit
End If
'Stop Error Resume Next
On Error GoTo 0
'The Microsoft OID Prefix used for the automated OID Generator
oidPrefix = "1.2.840.113556.1.8000.2554"
'Split GUID into 6 hexadecimal numbers
guidPart0 = Trim(Mid(guidString, 2, 4))
guidPart1 = Trim(Mid(guidString, 6, 4))
guidPart2 = Trim(Mid(guidString, 11, 4))
guidPart3 = Trim(Mid(guidString, 16, 4))
guidPart4 = Trim(Mid(guidString, 21, 4))
guidPart5 = Trim(Mid(guidString, 26, 6))
guidPart6 = Trim(Mid(guidString, 32, 6))
'Convert the hexadecimal to decimal
oidPart0 = CLng("&H" & guidPart0)
oidPart1 = CLng("&H" & guidPart1)
oidPart2 = CLng("&H" & guidPart2)
oidPart3 = CLng("&H" & guidPart3)
oidPart4 = CLng("&H" & guidPart4)
oidPart5 = CLng("&H" & guidPart5)
oidPart6 = CLng("&H" & guidPart6)
'Concatenate all the generated OIDs together with the assigned Microsoft prefix and return
GenerateOID = oidPrefix & "." & oidPart0 & "." & oidPart1 & "." & oidPart2 & "." & oidPart3 & _
"." & oidPart4 & "." & oidPart5 & "." & oidPart6
End Function
'Output the resulted OID with best practice info
Wscript.Echo "Your root OID is: " & VBCRLF & GenerateOID
10. Double click the .vbs file and it will generate a unique ID. Note this ID and type it in Unique X500 Object ID. To copy this Object ID to your clipboard, click on the output box and press Ctrl+C. You can then paste it into any text file.
11. Under Syntax field select type of data the attribute will hold. As per our example, Campus Name would hold String value. So, we will select Unicode String from dropdown. If you believe that the attribute will hold multiple values, enable the checkbox Multi-Valued. You can also specify the Minimum and Maximum length. 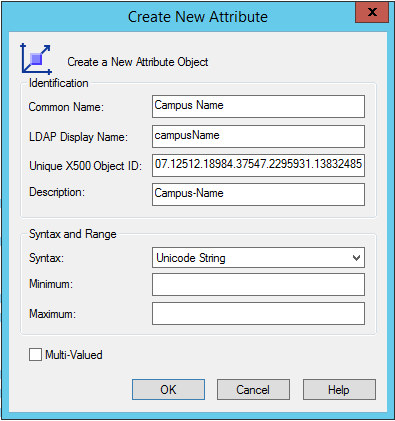
12. After filling up the information, click OK.
13. Now your newly created attribute will be available under Attributes. 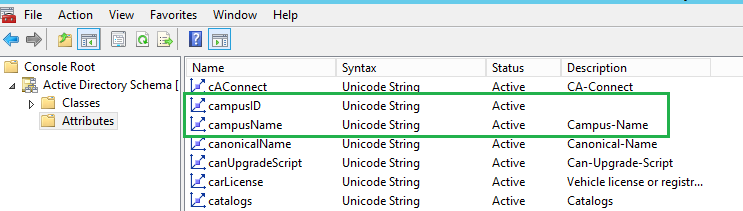
Keep the mmc console open as you will again need it to assign the attributes to User class.
Assigning Custom Attributes To User class
You have just created the attributes but these attributes must be assigned to user class before you can set these attributes via Active Directory Users and Computers tool.
To assign newly created attributes to User class follow the steps below:
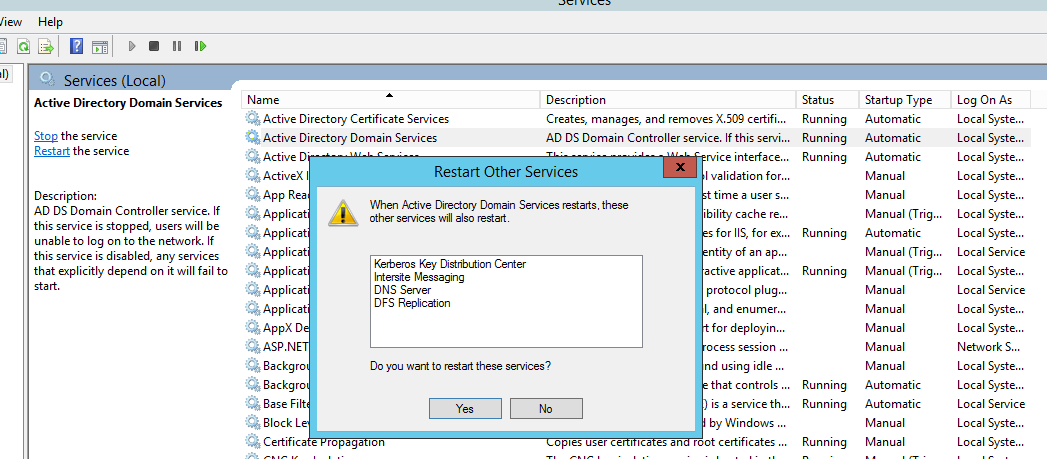
- Go to Classes node in console and select user
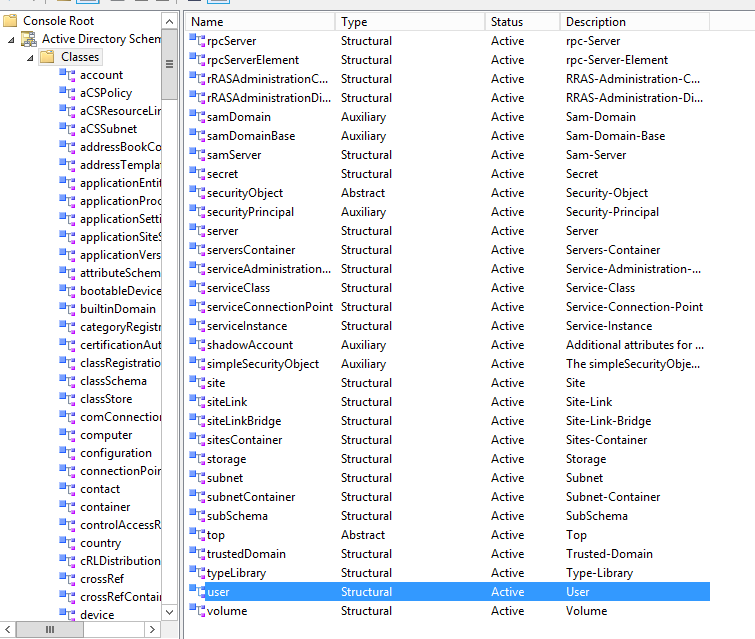
2. Right click User class and select Properties.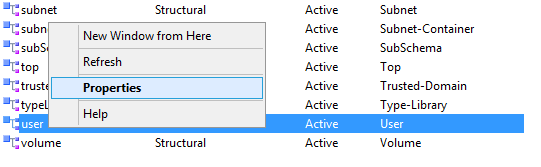
3. On user properties window, go to Attributes tab

4. Click Add button and select the newly created attributes (Campus Name). In the similar manner, add the remaining attributes you created previously and click OK.
5. Now wait for sometime so that the new attributes get replicated to all DCs.
Restarting Active Directory Domain Services
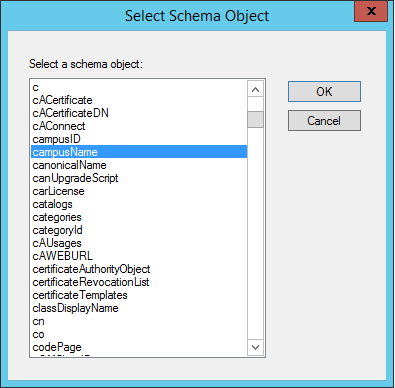
Now that you have successfully created custom attributes, you need to restart the Active Directory Domain Services for schema changes to take effect.
- Press the keys ‘Windows‘+ ‘R‘ to open Run dialog.
- Type the command services.msc and hit OK.
- Right click the Active Directory Domain Services service, click Restart. When prompted, click Yes to restart all the dependent services.
Verify new attributes in Active Directory Users and Computers
To verify if new attributes are available to be set for users, open Run dialog and type dsa.msc to open Active Directory Users and Computers console.
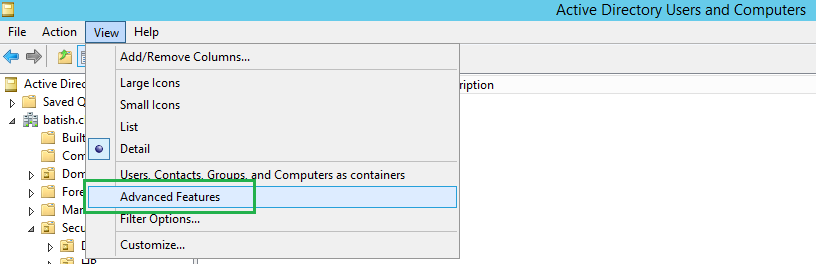
- By default, Active Directory Users and Computers console does not show Attribute editor under user properties. To active this option, click View menu option and select Advanced Features.
 2. Now right click any user account and select Properties
2. Now right click any user account and select Properties
3. On user properties window, select Attribute Editor Scroll down to see your custom attribute. 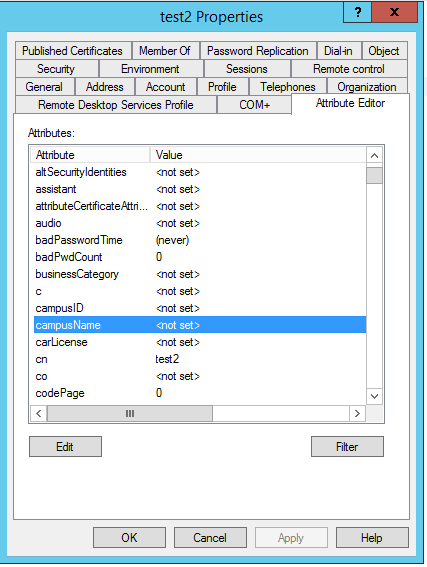
4. Double click the attribute name to set its value and click OK to save.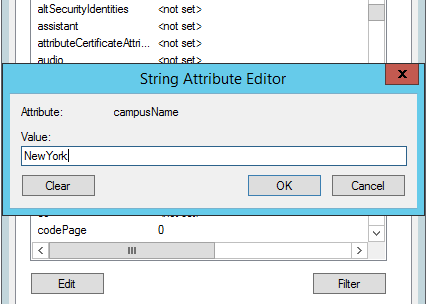
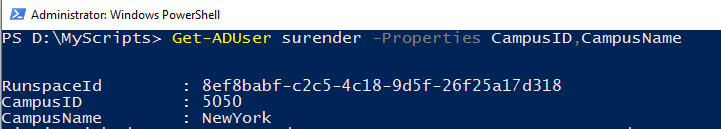
Manipulating Custom Attributes via Windows PowerShell
To set the value of any attribute, launch the Windows PowerShell console. Type the following command:
Set-ADUser surender -Add @{CampusID="5060"; CampusName="NewYork"}
Of course, replace the username surender with your own user.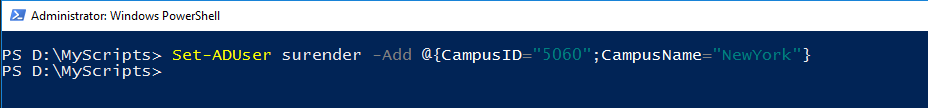
To replace or modify the values, use the following command:
Set-ADUser surender -Replace @{CampusID="5050"; CampusName="Delhi"}
To delete the values of custom attribute, use the following command:
Set-ADUser surender -Remove @{CampusID="5050"; CampusName="Delhi"}
To list the custom attributes for a particular user, use the following command:
Get-ADUser username -Properties CampusID, CampusName
This is how you can modify the Active Directory Schema if your organizational requirement want you to add custom attributes that are not available in Active Directory by default. Once again, please note that schema changes that you make are permanent and cannot be reversed.
9 Comments
Comments are closed.




Excellent article. I was looking for such article so that I could modify AD schema to fit our need
Great Article, It has everything that needs to be done step by step. Thanks a lot !!
Thanks for your feedback 🙂
Do I need to restart the AD services on all the Domain controllers ?
No need to do it on all DCs; just restart the services on PDC role holder. It will take time to replicate depending on nos of DCs you have.
Perfect instructions to get custom properties in Active directory users. Thank you author!
Thank you for your kind words!
Cheers 🙂
Hi,
Thanks for the detailed guide and how to i bulk update the different value in custom attribute from csv?
Rgds
Chanchal
Hi,
Here is the idea:
$Users = Import-Csv -Path D:\ADUsers.csvforeach ($User in $Users) {
#Search in particular OU and set the Attributes
Get-ADUser -Filter "SamAccountName -eq '$($User.SamAccountName)'" -Properties * -SearchBase "cn=Users,DC=domain,DC=local" |
Set-ADUser -Replace @{CampusName="$User.CampusName"} -Verbose
}
You need to adjust this snippet for your environment.