- August 11, 2015
- Posted by: Surender Kumar
- Category: Windows Server
Active Directory Fundamentals
Table of Contents
Active Directory is a hierarchical database that holds information about the network’s resources such as computers, servers, users, groups and more. The main purpose of Active Directory is to provide central authentication and authorization services. Normal administrative tasks when working with Active Directory include creating, managing, moving, editing and sometimes – deleting – various objects such as user accounts, computer accounts, groups, contacts and other objects. The Active Directory database is stored on Domain Controllers (or DCs), in a file called NTDS.DIT.
Do I Need Active Directory?
Active Directory is the database (think of a directory as a collection of information, like a phone book), whereas a domain controller is a single computer or server that controls Active Directory. There are typically multiple domain controllers that host Active Directory. How do you know if you need Active Directory? There are factors that you should address to determine whether you should go for the installation of a domain controller. Following are some of the questions you should ask yourself:
- Do I want to centrally manage access to resources such as users, computers, printers and groups?
- Do I want to control user accounts from one location?
- Do I have applications that rely on Active Directory?
If you answered “YES” to any of these questions, you undoubtedly will want to take advantage of the features that Active Directory provides. Taking each one of the questions into account, you will find that your life as an administrator will be much easier if you use Active Directory.
To get a good understanding of how Active Directory works, you must first understand what the Schema is and the role it plays in the directory service.
Active Directory Schema
The schema is the Active Directory component that defines all the objects and attributes that the directory service uses to store data. The physical structure of the schema consists of the object definitions. The schema itself is stored in the directory.
In general words, the schema is a structured framework or plan which acts as the building blocks of Active Directory, much like DNA molecules are the building blocks for our bodies. The schema defines how each attribute can be used and the properties associated with the attribute.
Schema Components
Objects, attributes, and classes are the basic components that are used to build object definitions in the schema.
Objects
Objects are structures that store both data that the objects represent and data that controls the content and structure of the objects. For example, a user account object contains a user’s logon name as well as data that indicates the proper syntax for storing the user’s logon name in the user object.
Active Directory uses objects to store data while the data is maintained in the directory. When the directory stores an object, some associated data is also stored along with the object. The extra data is stored in the attributes of the object.
Attributes
Attributes contain data that defines the information that is stored in an object or in another attribute. For example, a user account object has attributes that store user information, such as the user’s first name, last name, password, office number, and telephone number. Different types of objects have different attributes. A printer object has attributes that store information that is related to printers, such as the printer model, the number of paper trays, the current location of the printer, and the port to which the printer is attached.
Some attributes contain information that relates to other attributes, such as syntax information or flags that label the attribute as optional or required. Syntax attributes define the format that is used to store data in other attributes. For example, because a telephone number comprises only digits, a syntax attribute might specify that the phone number attribute can only store digits 0 through 9, and letters of the alphabet are prohibited. Active Directory uses syntax attributes to ensure that information is stored in a legitimate format and that the information is a valid data type.
Attributes can be required or optional. A user account object requires a user name attribute and a password attribute, although the office number attribute is optional. That is, a user account cannot be used without a user name; however, it can be used without an office number. The office number attribute is included for convenience, and it is considered an optional attribute.
Classes
Object definitions are categorized into groups that are called classes. Classes act as blueprints that can be used each time a new object is created. When a new object is created in the directory, the object’s class determines the attributes that are associated with the new object, including which attributes are required and which attributes are optional.
Active Directory has predefined classes that define all of the different object type’s that the directory needs to function properly. For example, when a new user account object is created in the directory, its definition comes from the classUser class. The class dictates that the new account object is required to have a user name attribute and a password attribute, and optionally it might have an office number attribute.
Object definitions are created by nesting classes inside one another. Nesting classes produces a parent/child relationship between the classes. Classes that are nested inside another class are referred to as subclasses. The parent of a subclass is referred to as a superclass. When one class is nested inside another, the nested class inherits the properties of the parent superclass. When various classes that contain particular attributes are nested inside another object class, a new object definition is created. Which classes are nested depends on which attributes are needed to define the new object type.
The schema stores class information, but it does not store the actual objects that are derived from a class. For example, when a new user account object is created, it is not stored in the schema. Active Directory looks up the user class in the schema. Active Directory then retrieves information regarding the object type and its associated attributes from the user class in the schema and uses that information to create the new user account object. When the new account is created, the data is stored in the new object, and Active Directory then writes the new account information into the directory database.
The Two Sides of Active Directory (AD)
Active Directory has both a logical side and a physical side, and each one plays a very important role. The physical side is made up of the domain controllers and physical locations where the domain controllers reside. When you promote a system to domain controller, you will usually place that domain controller close to the user population that will use it for authentication and access. Domain controllers need to communicate with one another to share the information they have.
The logical side is a little more nebulous; as well as containing the objects that define how the resources are organized and accessed, the logical side contains objects within Active Directory that define how the domain controllers will communicate with one another. Active Directory sites and site links define which domain controllers will replicate directly with each other and which ones will have to communicate indirectly through other domain controllers.
Domains dictate the replication scope. When you create a domain, the domain partition is replicated only to domain controllers from the same domain. The domain partition is not copied to domain controllers outside of the domain. This allows you to partition your directory service and reduce the size of the database file that holds all of the forest’s objects.
Organizational units are used to organize objects for easy administration and to manage those objects easily using group policies. To have efficient administration of resources, you should design your Active Directory with administration in mind.
Active Directory Partitions
The AD database is divided up into partitions for replication and administration. Each Domain Controller (DC) has a copy of the Active Directory database store in a file called NTDS.DIT. The data in this file is divided into partitions. The partition type determines how it will be replicated throughout the forest. For example, the domain partition is only replicated to Domain Controllers in that domain, while the Global Catalog partition is replicated to all Domain Controllers in the forest.
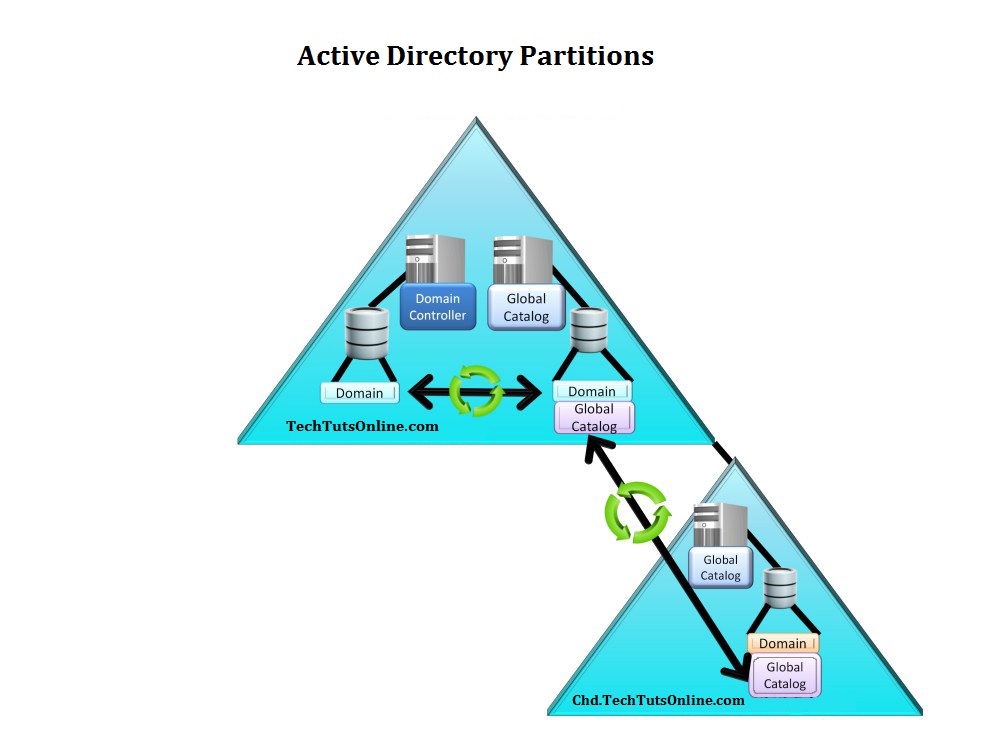
- Domain Partition : The momain partition is replicated only to Domain Controllers in that domain. Active Directory Users and Computers obtains it data from this partition. All Domain Controllers in that domain replicate changes to each other regardless of whether the Domain Controller is a global catalog server.
- Global Catalog Partition : This partition is also referred to as Partial Attribute Set (PAS) in some documents. The partition contains a partial replica of all objects in the domain. It is replicated to all Global Catalog Servers in the forest.
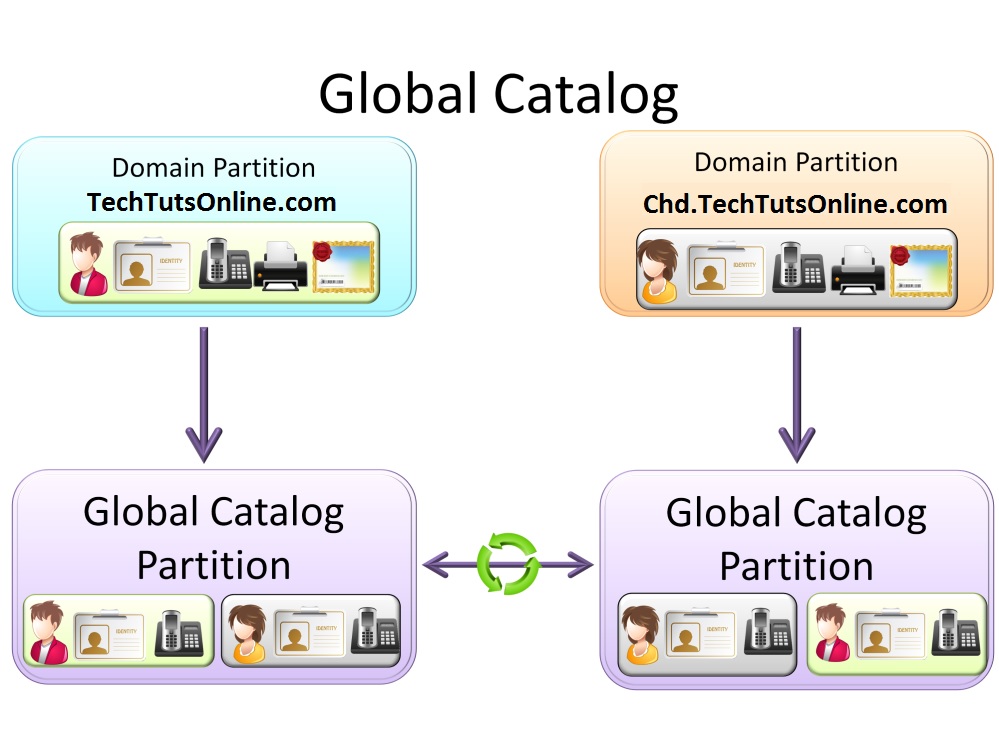
The Global Catalog Partition is created automatically by software on the Domain Controller. This software copies some of the attributes for each object in the Global Catalog Partition. This information is replicated to other Domain Controllers inside and outside the domain. In this way, all the Global Catalog servers will have a partial replica of all objects in the domain.
- Schema Partition : The schema partitions define what can be stored in the Active Directory database. It essentially defines the layout of the database. The schema partition is replicated to all Domain Controllers in the forest and defines the Active Directory database for all Domain Controllers in the domain.
- Configuration Partition : The configuration partition contains configuration information for the whole forest. For example, it contains information about sites in the forest and partition defined in the Active Directory database. This partition is replicated to all Domain Controllers in the forest.
- Application Partition : The application partition is created by applications to store their data. It is different from any other partition in that the application can choose which Domain Controller or Controllers to store the data on. The advantage for the application storing the data this way is that the application has access to the same replica and fault tolerance used by the Domain Controllers. An example of an Application is DNS Integrated Active Directory Zones. When this zone type is used, the data is stored in an application partition.
New Features in Windows Server 2008
With the release of Windows Server 2008, several enhancements are done in Active Directory and some items have simply been renamed while other technologies have been moved into the Active Directory family.
- The Active Directory is now known as Active Directory Domain Services (AD DS). AD DS stores all information about resources on the network, such as users, computers, and other devices.
- Active Directory Lightweight Directory Services (AD LDS) is the latest version of Active Directory Application Mode (ADAM).
- Active Directory Federation Services (AD FS) provides Web single sign-on (SSO) technologies to authenticate users to multiple web applications in a single session.
- Active Directory Rights Management Services (AD RMS) is an information-protection technology that works with RMS-enabled applications to protect and secure information from unauthorized use online and offline, inside and outside of the environment.
- Active Directory Certificate Services (AD CS) allows the mapping of users and resources to a private key to help secure identity in a Public Key Infrastructure (PKI)-based environment.
Along with renaming and restructuring these technologies, Microsoft (MS) also updated all of the existing Active Directory technologies. Following are some of the major updates to Active Directory:
- Read-Only Domain Controller (RODC)
- Windows Server Core
Read-Only Domain Controller
The RODC contains a read-only copy of the Active Directory database that cannot be directly configured. This increases security, especially in areas where the physical security of the domain controller cannot be guaranteed.
A new Domain Name System (DNS) zone was also created to support this new server type. A primary read-only zone contains read-only copies of the domain partition, ForestDNSZones, and DomainDNSZones.
Windows Server Core
Windows Server Core has introduced a new edition of Windows Server titled “Server Core”. Server Core is a Windows server which is fully command-line based and does not possess a GUI. All administration of Server Core is performed via the command line or via scripting. You may also administer some functions by connecting to Server Core from another server’s Microsoft Management Console (MMC) utility.
Server Core was introduced for many reasons:
- Reduced maintenance: Server Core installs only what is necessary for the specific server role.
- Reduced attack surface: Because Server Core installs only necessary services for the specific server role, so the attack surface is reduced.
- Reduced management: Because fewer applications are running on the server, there is less to manage.
- Less disk space: Server Core can run on less than 5 GB of disk space.
Server Manager
At first glance, Server Manager seems to be just another attempt by Microsoft to put some things together that they think would be in our ideal tool chest. I dismissed it in the beginning, but after working with it for a while, it has become one of my favorite new features of Server 2008 and above. When you first launch Server Manager, you are greeted with a summary page that displays a high-level summary of the server, the roles on that server, the features that are configured on that server, and resources and support.
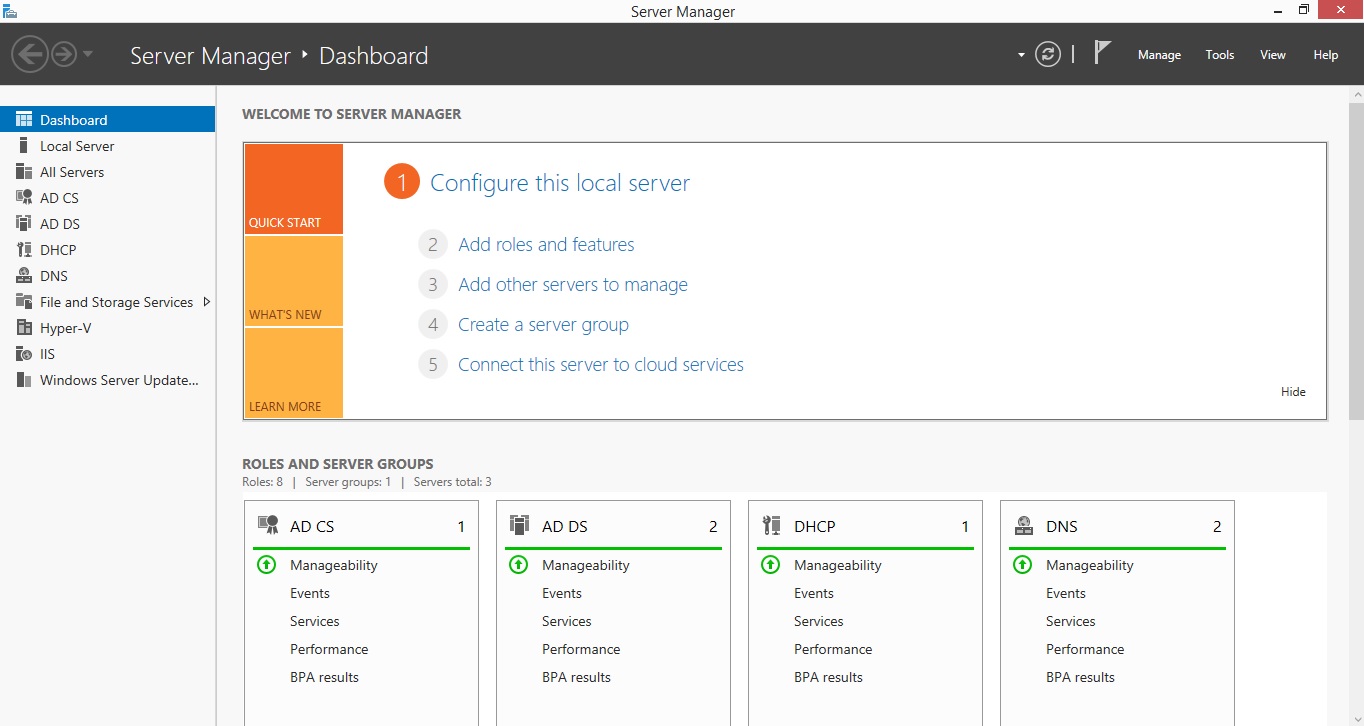
This is how Server Manager looks like in Windows Server 2012 R2 which is the latest available version in Microsoft Windows Server family.


