- July 23, 2015
- Posted by: Surender Kumar
- Category: Cisco Routers
Gateway Load Balancing Protocol
Table of Contents
Gateway Load Balancing Protocol (GLBP) is a more recent proprietary standard first hop redundancy protocol from Cisco that permits load balancing as well as redundancy.
The Gateway Load Balancing Protocol feature provides automatic router redundancy for IP hosts configured with a single default gateway in a network. Multiple first hop routers on the LAN combine to offer a single virtual first hop IP router while sharing the IP packet forwarding load. Other routers on the LAN may act as redundant GLBP routers that will become active if any of the existing forwarding routers fail.
How GLBP Works
GLBP performs a similar, but not identical, function for users as HSRP and VRRP. HSRP and VRRP protocols allow multiple routers to participate in a virtual router group configured with a virtual IP address. One member is elected to be the Active router to forward traffic destined to the virtual IP address for the group. The other routers in the group are redundant until the Active router fails. The Standby routers’ bandwidth remain unused. But GLBP provides load balancing over multiple gateways using a single virtual IP address and multiple virtual MAC addresses. Each host is configured with the same virtual IP address, and all routers in the virtual router group participate in forwarding packets. GLBP members communicate between each other through hello packets sent every 3 seconds to the multicast address 224.0.0.102, UDP port 3222 (source and destination).
Comparison between HSRP, VRRP and GLBP:
| Protocol Features | HSRP (Hot Standby Router Protocol) | VRRP (Virtual Router Redundancy Protocol) | GLBP (Gateway Load Balancing Protocol) |
| Router Roles | 1 router Active. 1 router Standby. 1 or more Listening |
1 router Master. 1 or more routers Backup | 1 Active Virtual Gateway (AVG). Upto 4 Active Virtual Forwarders (AVF) |
| Scope | Cisco Proprietary | IEEE Standard | Cisco Proprietary |
| Election | Active Router: Highest Priority or Highest IP |
Master Router: Highest Priority or Highest IP |
Active Virtual Gateway: Highest Priority or Highest IP |
| Tracking support |
Yes |
Yes |
Yes |
| Preempt Support | Yes (by default disabled) | Yes (by default enabled) | Yes (by default disabled) |
| Timer Adjustment |
Possible |
Possible |
Possible |
| Traffic Type | Multicast to 224.0.0.2 – udp 1985 (version1) 224.0.0.102 – udp 1985 (version2) |
Multicast to 224.0.0.18 – IP type 112 | Multicast to 224.0.0.102 udp 3222 |
| Load Balancing | Requires appropriate distribution of Virtual GW IP per Clients for optimal load-balancing | Requires appropriate distribution of Virtual GW IP per Clients for optimal load-balancing | Clients are transparently updated with virtual MAC according to load-balancing algorithm through ARP requesting a unique virtual gateway |
Active Virtual Gateway (AVG)
Members of a GLBP group elect one gateway to be the Active Virtual Gateway (AVG) for that group and other group members act as Active Virtual Forwarders (AVF) providing backup to AVG when AVG becomes unavailable. The AVG assigns a virtual MAC address to each member of the GLBP group. Each gateway assumes responsibility for forwarding packets sent to the virtual MAC address assigned to it by the AVG. These gateways are known as active virtual forwarders (AVFs) for their virtual MAC address. GLBP gateway priority determines the role that each GLBP gateway plays and what happens if the AVG fails.
The AVG is responsible for answering Address Resolution Protocol (ARP) requests for the virtual IP address. Load sharing is achieved by the AVG replying to the ARP requests with different virtual MAC addresses.
Virtual Gateway Redundancy
GLBP operates virtual gateway redundancy in the same way as HSRP. One gateway is elected as the AVG, another gateway is elected as the standby virtual gateway (SVG), and the remaining gateways are placed in a listen state.
If an AVG fails, the standby virtual gateway will assume responsibility for the virtual IP address. A new standby virtual gateway is then elected from the gateways in the listen state.
GLBP Load Balancing Algorithm
GLBP load balancing is done in one of three ways:
- Round-robin load-balancing: Each router MAC address is used sequentially to respond to ARP requests. This is the default load balancing mode in GLBP and is suitable for any number of clients.
- Weighted load-balancing: Traffic is balanced proportional to a configured weight. Each GLBP router in the group advertise its weightage and assignment; the AVG will act based on that value. For example, if there are two routers R1 and R2 in a group and R1 has double the forwarding capacity than router R2, the weighting value of router R1 should be configured to be double the amount of R2.
- Host-dependent load-balancing: A given host always uses the same router.
GLBP Configuration
I will use the following network diagram to demonstrate GLBP configuration
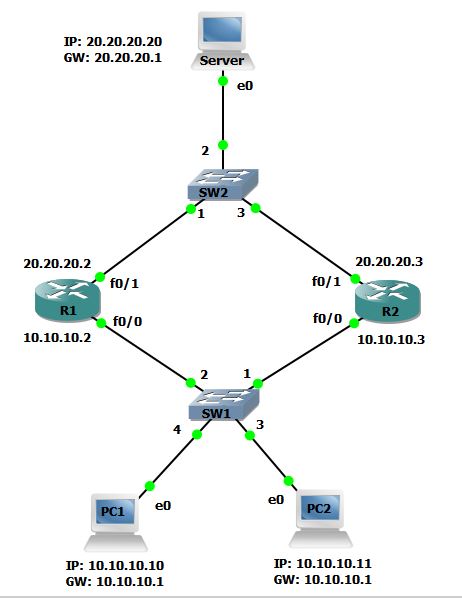 PC1 and PC2 are configured with 10.10.10.1 as gateway. 10.10.10.1 is a virtual IP address which is supported on both routers (R1 and R2) configured with GLBP.
PC1 and PC2 are configured with 10.10.10.1 as gateway. 10.10.10.1 is a virtual IP address which is supported on both routers (R1 and R2) configured with GLBP.
R1 Configuration
R1#conf t Enter configuration commands, one per line. End with CNTL/Z. R1(config)#int fa0/0 R1(config-if)#ip address 10.10.10.2 255.255.255.0 R1(config-if)#no shut R1(config-if)#glbp 1 ip 10.10.10.1 R1(config-if)# *Jul 23 14:52:58.355: %GLBP-6-STATECHANGE: FastEthernet0/0 Grp 1 state Standby -> Active R1(config-if)# *Jul 23 14:53:08.355: %GLBP-6-FWDSTATECHANGE: FastEthernet0/0 Grp 1 Fwd 1 state Listen -> Active R1(config-if)#glbp 1 priority 110 R1(config-if)#glbp 1 authentication md5 key-string Abc@123 R1(config-if)#glbp 1 preempt R1(config-if)#int fa0/1 R1(config-if)#ip address 20.20.20.2 255.255.255.0 R1(config-if)#no shut R1(config-if)#glbp 2 ip 20.20.20.1 R1(config-if)#end R1#
The glbp 1 ip 10.10.10.1 command create GLBP group 1 and assigns virtual IP address on selected interface. The glbp 1 authentication md5 key-string command is used to provide MD5 secure password so that only authenticated router can participate in GLBP group. Other options like preempt, priority etc are same as HSRP and VRRP.
R2 Configuration
R2#conf t Enter configuration commands, one per line. End with CNTL/Z. R2(config)#int fa0/0 R2(config-if)#ip add 10.10.10.3 255.255.255.0 R2(config-if)#no shut R2(config-if)#glbp 1 ip 10.10.10.1 R2(config-if)# *Jul 23 15:13:03.135: %GLBP-4-BADAUTH: Bad authentication received from 10.10.10.2, group 1 R2(config-if)#glbp 1 authentication md5 key-string Abc@123 R2(config-if)# *Jul 23 15:13:23.139: %GLBP-6-STATECHANGE: FastEthernet0/0 Grp 1 state Standby -> Active *Jul 23 15:13:26.439: %GLBP-6-STATECHANGE: FastEthernet0/0 Grp 1 state Active -> Speak *Jul 23 15:13:42.471: %GLBP-6-FWDSTATECHANGE: FastEthernet0/0 Grp 1 Fwd 2 state Listen -> Active R2(config-if)#glbp 1 preempt R2(config-if)#int fa0/1 R2(config-if)#ip add 20.20.20.3 255.255.255.0 R2(config-if)#no shut R2(config-if)#glbp 2 ip 20.20.20.1 R2(config-if)#end R2#
GLBP Verification
Let’s now see the status of GLBP
R1#show glbp FastEthernet0/0 - Group 1 State is Active 2 state changes, last state change 00:25:55 Virtual IP address is 10.10.10.1 Hello time 3 sec, hold time 10 sec Next hello sent in 1.132 secs Redirect time 600 sec, forwarder time-out 14400 sec Authentication MD5, key-string "Abc@123" Preemption enabled, min delay 0 sec Active is local Standby is 10.10.10.3, priority 100 (expires in 9.196 sec) Priority 110 (configured) Weighting 100 (default 100), thresholds: lower 1, upper 100 Load balancing: round-robin Group members: ca01.1dbc.0008 (10.10.10.2) local ca02.1108.0008 (10.10.10.3) authenticated There are 2 forwarders (1 active) Forwarder 1 State is Active 1 state change, last state change 00:25:45 MAC address is 0007.b400.0101 (default) Owner ID is ca01.1dbc.0008 Redirection enabled Preemption enabled, min delay 30 sec Active is local, weighting 100 Arp replies sent: 1 Forwarder 2 State is Listen MAC address is 0007.b400.0102 (learnt) Owner ID is ca02.1108.0008 Redirection enabled, 598.764 sec remaining (maximum 600 sec) Time to live: 14398.572 sec (maximum 14400 sec) Preemption enabled, min delay 30 sec Active is 10.10.10.3 (primary), weighting 100 (expires in 9.748 sec) [output cut]
For GLBP group 1, there are 2 forwarders and one is Active and one is in Listen State. By default, GLBP use round-robin algorithm for load-balancing.
Load Balancing Verification
To check if Load-balancing is working, I will first go to PC1 and run a trace to Server 20.20.20.20. Then I will check the ARP cache and note the MAC address.
PC1> trace 20.20.20.20 trace to 20.20.20.20, 8 hops max, press Ctrl+C to stop 1 10.10.10.2 9.272 ms 32.860 ms 10.133 ms 2 20.20.20.20 43.135 ms PC1> show arp 00:07:b4:00:01:01 10.10.10.1 expires in 107 seconds
The MAC address resolved on PC1 is 00:07:b4:00:01:01 which is a virtual MAC address assigned to router R1’s physical interface fastEthernet0/0 (ca01.1dbc.0008) as we have seen under show glbp command output above.
This means the PC1 is going to Server via R1. Now, lets check from PC2
PC2> trace 20.20.20.20 trace to 20.20.20.20, 8 hops max, press Ctrl+C to stop 1 10.10.10.3 3.153 ms 35.896 ms 21.190 ms 2 20.20.20.20 21.169 ms PC2> show arp 00:07:b4:00:01:02 10.10.10.1 expires in 105 seconds
PC2 is going to Server via R2. The GLBP automatically balances the load between both routers. You can also set load-balancing algorithm to Weighted by using glbp 1 load-balancing weighted command.
Virtual Gateway Redundancy Verification
We have checked the load-balancing is working. Now it is time to check what GLBP will do if one of the virtual gateway goes down. I will go to R1 and shutdown the interface fastEthernet0/0.
R1#conf t Enter configuration commands, one per line. End with CNTL/Z. R1(config)#int fa0/0 R1(config-if)#shut R1(config-if)# *Jul 23 15:57:20.815: %GLBP-6-FWDSTATECHANGE: FastEthernet0/0 Grp 1 Fwd 1 state Active -> Init *Jul 23 15:57:20.819: %GLBP-6-STATECHANGE: FastEthernet0/0 Grp 1 state Active -> Init R1(config-if)#
The GLBP status on R1 changed to Init State but PC1 and PC2 can still reach Server via R2.
PC1> trace 20.20.20.20 trace to 20.20.20.20, 8 hops max, press Ctrl+C to stop 1 10.10.10.3 11.219 ms 10.199 ms 32.174 ms 2 20.20.20.20 45.968 ms PC1>
PC2> trace 20.20.20.20
trace to 20.20.20.20, 8 hops max, press Ctrl+C to stop
1 10.10.10.3 1.077 ms 11.046 ms 10.281 ms
2 20.20.20.20 65.278 ms
This concludes the R2 is now working as AVG and still forwarding the traffic destined for virtual IP 10.10.10.1. When the router R1 will come online again, both will start load-balancing the traffic as they were doing before.
You can also use SLA probe with GLBP to track the status of interface as we did in VRRP configuration section. Follow the steps below to create SLA monitor and add track based weighting under GLBP interface.
R1#conf t Enter configuration commands, one per line. End with CNTL/Z. R1(config)#ip sla monitor 1 R1(config-sla-monitor)#type echo protocol ipicmpEcho 20.20.20.20 source-interface fa0/1 R1(config-sla-monitor-echo)#timeout 1000 R1(config-sla-monitor-echo)#frequency 3 R1(config-sla-monitor-echo)#exit R1(config)#ip sla monitor schedule 1 life forever start-time now R1(config)#track 1 rtr 1 reachability R1(config-track)#exit R1(config)#int fa0/0 R1(config-if)#glbp 1 load-balancing weighted R1(config-if)#glbp 1 weighting track 1 decrement 10 R1(config-if)#end R1#
Now, see the GLBP status using show glbp command.
R1#show glbp FastEthernet0/0 - Group 1 State is Active 4 state changes, last state change 00:06:52 Virtual IP address is 10.10.10.1 Hello time 3 sec, hold time 10 sec Next hello sent in 1.084 secs Redirect time 600 sec, forwarder time-out 14400 sec Authentication MD5, key-string "Abc@123" Preemption enabled, min delay 0 sec Active is local Standby is 10.10.10.3, priority 100 (expires in 9.088 sec) Priority 110 (configured) Weighting 100 (default 100), thresholds: lower 1, upper 100 Track object 1 state Up decrement 10 Load balancing: weighted Group members: ca01.1dbc.0008 (10.10.10.2) local ca02.1108.0008 (10.10.10.3) authenticated There are 2 forwarders (1 active) Forwarder 1 State is Active 3 state changes, last state change 00:06:24 MAC address is 0007.b400.0101 (default) Owner ID is ca01.1dbc.0008 Redirection enabled Preemption enabled, min delay 30 sec Active is local, weighting 100 Arp replies sent: 4 Forwarder 2 State is Listen MAC address is 0007.b400.0102 (learnt) Owner ID is ca02.1108.0008 Redirection enabled, 597.024 sec remaining (maximum 600 sec) Time to live: 14399.792 sec (maximum 14400 sec) Preemption enabled, min delay 30 sec Active is 10.10.10.3 (primary), weighting 100 (expires in 9.216 sec) Arp replies sent: 2 [output cut]
Did you notice that the load-balancing algorithm is now changed to weighted? And now if the link between R1’s fastEthernet0/1 and Server goes down, the SLA probe will return false and the track object will start failing which will kick the router R1 to the decrement its weighting by 10. Then the router R2 will automatically take over R1. I will first enable debugging for glbp on R1. Then I will shutdown the interface fa0/1.
R1#debug glbp terse GLBP: GLBP Errors debugging is on GLBP Events debugging is on (protocol, redundancy, track) GLBP Packets debugging is on (Request, Reply) R1#conf t Enter configuration commands, one per line. End with CNTL/Z. R1(config)#int fa0/1 R1(config-if)#shut R1(config-if)# *Jul 23 17:12:44.826: GLBP: Fa0/1 Interface down *Jul 23 17:12:44.826: GLBP: Fa0/1 2.1 Active: e/Forwarder disabled *Jul 23 17:12:44.826: GLBP: Fa0/1 2.1 Active -> Init *Jul 23 17:12:44.826: %GLBP-6-FWDSTATECHANGE: FastEthernet0/1 Grp 2 Fwd 1 state Active -> Init R1(config-if)# *Jul 23 17:12:44.830: GLBP: Fa0/1 2.2 Listen: e/Forwarder disabled *Jul 23 17:12:44.830: GLBP: Fa0/1 2.2 Listen -> Init *Jul 23 17:12:44.830: GLBP: Fa0/1 2 Standby: e/GLBP disabled *Jul 23 17:12:44.834: GLBP: Fa0/1 2 Active router IP is unknown, was 20.20.20.3 *Jul 23 17:12:44.834: GLBP: Fa0/1 2 Standby router is unknown, was local *Jul 23 17:12:44.834: GLBP: Fa0/1 2 Standby -> Init *Jul 23 17:12:52.610: GLBP: Fa0/0 1 Track 1 object changed, state Up -> Down *Jul 23 17:12:52.610: GLBP: Fa0/0 1 Weighting 100 -> 90 R1(config-if)#
As soon as interface fa0/1 goes down, track 1 object status changed from Up to Down and the Weighting is decremented from 100 to 90.
PCs can still reach the Server via R2 because R2 is now AVG with higher weighting (100).
PC1> ping 20.20.20.20
84 bytes from 20.20.20.20 icmp_seq=1 ttl=63 time=18.265 ms
84 bytes from 20.20.20.20 icmp_seq=2 ttl=63 time=14.205 ms
84 bytes from 20.20.20.20 icmp_seq=3 ttl=63 time=35.382 ms
84 bytes from 20.20.20.20 icmp_seq=4 ttl=63 time=49.240 ms
84 bytes from 20.20.20.20 icmp_seq=5 ttl=63 time=39.281 ms
This concludes Gateway Load Balancing Protocol section.


