- July 7, 2015
- Posted by: Surender Kumar
- Category: Network Basics
Cisco Three Layer Hierarchical Model
Large networks can be extremely complicated, with multiple protocols, detailed configurations, and diverse technologies. Hierarchical approach helps us summarize a complex collection of details into an understandable model. Then, as specific configurations are needed, the model dictates the appropriate manner in which to apply them.
The Cisco Three-Tier (Three Layer) hierarchical network model, can help you design, implement and maintain a scalable, cost-effective, reliable hierarchical network. Cisco
defines three layers, as shown below
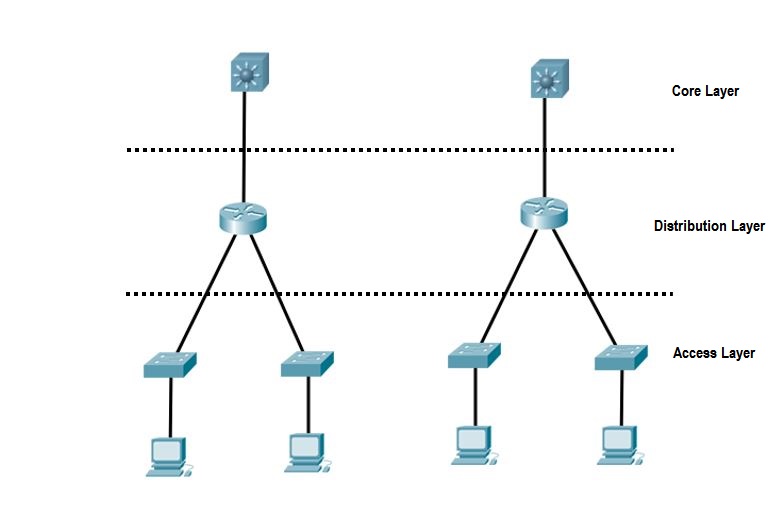 Each layer has specific responsibilities. However, the three layers are logical and do not necessarily represents the arrangement of physical devices.
Each layer has specific responsibilities. However, the three layers are logical and do not necessarily represents the arrangement of physical devices.
The Core Layer
The core layer is generally the core of the network. At the top of the hierarchy, the core layer is responsible for transporting large amounts of traffic
both reliably and quickly. The only purpose of the network’s core layer is to switch traffic as fast as possible. The traffic transported across the core is common to a majority of users. However, remember that user data is processed at the distribution layer, which forwards the requests to the core if needed.
If there is a failure in the core, every single user can be affected. Therefore, fault tolerance at this layer is a priority. The core is likely to see large volumes of traffic, so speed and latency are driving concerns here.
Do’s while designing the Core:
- Design the core for high reliability. Consider data-link technologies that facilitate both speed and redundancy, such as Gigabit Ethernet (with redundant links), or even 10Gigabit Ethernet.
- Design with speed in mind. The core should have least latency as possible.
- Select routing protocols with lower convergence times.
Don’ts while designing the Core:
- Never use any access lists, routing between virtual local area networks (VLANs), and packet filtering etc since this can slow down the traffic.
- Don’t support workgroup access here.
- Avoid expanding the core (i.e. adding routers, switches) when the network grows. If performance becomes an issue in the core, give preference to upgrades rather than expansion.
The Distribution Layer
The distribution layer is also referred to as the workgroup layer and is the communication point between the access layer and the core. The primary functions of the distribution layer are to provide routing, filtering and WAN access and to determine how packets can access the core, if needed. The distribution layer must determine the fastest way that network service requests are handled – for example, how a file request is forwarded to a server. After the distribution layer determines the best path, it forwards the request to the core layer if necessary. The core layer then quickly transports the request to the correct service.
The distribution layer is the place to implement policies for the network. Here you can exercise considerable flexibility in defining network operation. There are several actions that generally should be done at the distribution layer:
- Routing
- Implementing access-lists, packet filtering and queuing
- Implementing security and network policies, including address translation and firewalls
- Redistributing between routing protocols, including static routing
- Routing between VLANs and other workgroup support functions
- Defining broadcast and multicast domains.
The Access Layer
The access layer controls user and workgroup access to internetwork resources. The access layer is sometimes referred to as the desktop layer. The network resources most users need will be available locally. The distribution layer handles any traffic for remote services. The following are some of the functions to be included at the access layer:
- Use of access control and policies
- Creation of separate collision domains (segmentation)
- Workgroup connectivity into the distribution layer.
Technologies such as Gigabit or Fast Ethernet switching are frequently seen in the access layer.


