- June 10, 2015
- Posted by: Surender Kumar
- Category: Windows Server
Active Directory Domain Services
Table of Contents
Active Directory is a hierarchical database that holds information about the network’s resources such as computers, servers, users, groups and more. The main purpose of Active Directory is to provide central authentication and authorization services. Normal administrative tasks when working with Active Directory include creating, managing, moving, editing and sometimes – deleting – various objects such as user accounts, computer accounts, groups, contacts and other objects. The Active Directory database is stored on Domain Controllers (or DCs), in a file called NTDS.DIT.Installing Active Directory is not all that difficult. However, once you get it installed, there is still plenty of work that needs to be done. The first stage of configuration of Active Directory is securing it. There are many areas that need attention and many settings that need to be altered to prepare it for secure action on your network. Let’s take a look at the initial settings that you should make to get Active Directory secure for your network before you dive into setting up the entire structure.
- Create a second administrative account for regular use.
- Set a complex and long password for the Administrator account.
- Rename the default Administrator account to some deceptive name.
- Set Password Policy in Default Domain Policy.
- Set Account Lockout Policy in Default Domain Policy.
- Create Organizational Unit(s) for User and Computer Accounts.
- Configure DNS properly to Forward queries and enable only secure dynamic updates.
- Use Best Practice Analyzer (BPA) for every Server Role (available in Windows Server 2008 R2 and above).
Active Directory Partitions
4. Configuration Partition: This partition contains configuration information for the whole forest. For example, it contains information about sites in the forest and partition defined in the Active Directory database. This partition is replicated to all Domain Controllers in the forest.
5. Application Partition: The application partition is created by Applications to store their data. It is different from any other partition in that the application can choose which Domain Controller or Controllers to store the data on. The advantage for the application storing the data this way is that the application has access to the same replicate and fault tolerance used by the Domain Controllers. An example of an Application is DNS Integrated Active Directory Zones.
Backup and Restore Active Directory on Server 2008 and above
Have you ever accidentally deleted a user account or an OU in Active Directory or Active Directory database become corrupted after Windows Updates?
So, How can you restore AD?
Let’s talk about how to backup AD in Windows Server 2008 and how to restore it:
Prerequisites: Getting Server 2008 Ready for Backup
Before you can backup Server 2008 you need to install the backup features from the Server Manager.
- To install the backup features click Start? Server Manager.
- Next click Features? Add Features
- Scroll to the bottom and select both the Windows Server Backup and the Command Line Tools
- Click Next, then click Install
Backing up Server 2008 Active Directory
Now that we have the backup features installed we need to backup Active Directory. You could do a complete server backup, but what if you need to do an authoritative restore of Active Directory?
As you’ll notice in Server 2008, there isn’t an option to backup the System State data through the normal backup utility.
We need to go “command line” to backup Active Directory.
- Open up your command prompt by clicking Start and type “cmd” and hit enter.
- In your command prompt type “wbadmin start systemstatebackup -backuptarget:D:” and press enter.
Note: You can use a different backup target of your choosing
- Type “y” and press enter to start the backup process.
When the backup is finished running you should get a message that the backup completed successfully. If it did not complete properly you will need to troubleshoot.
You have successfully completed the backup.
So now what if you accidentally delete an OU, group, or a user account and it’s already replicated to your other servers? We will need to perform an authoritative restore of the Active Directory object you accidentally deleted.
Authoritative Restore of Active Directory
- To do this you will need to boot into DSRM (Directory Services Restore Mode) by restarting your server and pressing F8during the restart.
- Choose Directory Services Restore Mode from the Advanced Boot menu.
- Login to your server with your DSRM password you created during Active Directory installation.
- Once you’re logged into your server and in DSRM safe mode, open a command prompt by clicking Start, type “cmd“, and press enter.
- To make sure you restore the correct backup it’s a good idea to use the “wbadmin get versions” command and write down the version you need to use.
- Now we need to perform a non-authoritative restore of Active Directory by typing “wbadmin start systemstaterecovery -version:04/14/2009-02:39“.
Note: The version of backup will vary depending on your situation. Type “y” and press enter to start the non authoritative restore.
- Wait for the restore to complete.
- You can mark the sysvol as authoritative by adding the –authsysvol switch to the end of the wbadmin command.
- But if you want to restore a specific Active Directory object then you can use the ever familiar ntdsutil.
For this example we are going to restore a user account with a distinguished name of CN=Test User,CN=Users,DC=xyz,DC=local. So the commands would be:
ntdsutil
activate instance ntds
authoritative restore
restore object “cn=Test User,cn=Users,dc=xyz,dc=local”
Note: The quotes are required
- Reboot your server into normal mode and you’re finished. The object will be marked as authoritative and replicate to the rest of your domain.
Active Directory Snapshots
Windows Server 2008 has a new feature called Active Directory Snapshots. Volume Shadow Copy Service now allows us to take a snapshot of Active Directory as a type of backup. In any case it’s a lot better than the alternative – taking down the DC, rebooting into DSRM, restoring the System State from a backup, and then exporting the attributes
With your Server working normally, open a command prompt by clicking Start, type “cmd“, and press enter.
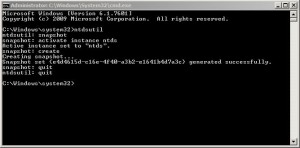
We are going to use the ntdsutil again for creating the Active Directory snapshots. The commands are:
ntdsutil
snapshot
activate instance ntds
create
quit
quit
 So now that you have a snapshot of AD, how do you access the data? First we need to mount the snapshot using ntdsutil. The commands are:
So now that you have a snapshot of AD, how do you access the data? First we need to mount the snapshot using ntdsutil. The commands are:
ntdsutil
snapshot
list all
mount 1 — (Note: You should mount the correct snapshot you need; for this example there is only 1.)
quit
quit
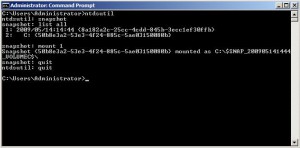 Your snapshot is mounted, but how do you access the data? We need to use the dsamain command to accomplish this. Then we need to select an LDAP port to use. The command is as follows:
Your snapshot is mounted, but how do you access the data? We need to use the dsamain command to accomplish this. Then we need to select an LDAP port to use. The command is as follows:
dsamain –dbpath c:\$SNAP_200905141444_VOLUMEC$\WINDOWS\NTDS\ntds.dit –ldapport 10001
The result should look like this:
 Now we need to go to Start, Administrative Tools, then Active Directory Users and Computers.
Now we need to go to Start, Administrative Tools, then Active Directory Users and Computers.
Right click Active Directory Users and Computers and select Change Domain Controller.
 In the area that says < Type a Directory Server name [:port] here > enter the name of your server and the LDAP port you used when running the dsamain command.
In the area that says < Type a Directory Server name [:port] here > enter the name of your server and the LDAP port you used when running the dsamain command.
For my example it would be: WIN-V22UWGW0LU8.HOME.LOCAL:10001
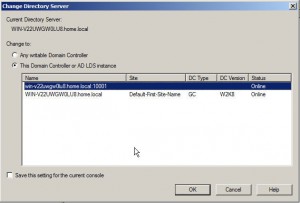 Now you can browse the snapshot of Active Directory without affecting anything else negatively.
Now you can browse the snapshot of Active Directory without affecting anything else negatively.
Active Directory Backup Strategy
It’s always good to have a solid backup plan for your Active Directory. You can use a combination of backup strategies or just one of these methods for backing up your Active Directory. Make sure you adapt your Active Directory backup strategy to meet your company’s needs and make it easy to recover if disaster strikes.


